Part 5: Environment Trust - Play Integrity & Attestation
A Staff-level architecture guide to securing the runtime environment against rooting, hooking frameworks, and emulators.
In Part 1, we designed the Stateless Blueprint. In Part 4, we secured the user’s identity with Passkeys. But there is a silent, systemic risk: What if the environment itself is compromised?
If your app is running on a rooted device with a hooking framework (like Frida or Xposed) or within a sophisticated emulator, even the best encryption and Passkeys can be undermined via memory injection or screen scraping. Today, we bridge the gap between “Who is the user?” and “Is the device trustworthy?”
⚡ TL;DR
- Compromised environments allow attackers to bypass local security controls and manipulate runtime logic.
- Play Integrity API provides a cryptographically signed verdict on app binary, device integrity, and licensing.
- Tiered Enforcement: Align your security requirements with business risk — reserving high-value actions for “Strong Integrity” environments.
- Operational Awareness: Play Integrity is quota-limited; calls should be strategically planned for login or high-risk checkpoints.
🛑 The Problem: The “Untrusted Sandbox”
For high-scale apps, a “clean” app binary is not enough if the ground it stands on is shifting.
- Instrumentation Frameworks: Tools like Frida can hook into your banking app’s methods at runtime to change a transfer destination or bypass a biometric check.
- Emulators & Device Farms: While Play Integrity helps detect virtualized environments, advanced emulators can still attempt to spoof lower integrity tiers to farm rewards or scrape data.
- Side-loading & Tampering: App Integrity verifies that the version running matches the one distributed via Google Play, helping you detect modded or re-signed APKs.
🏛️ Play Integrity API
The Play Integrity API (the successor to SafetyNet) allows your app to request a signed token from Google.
🔄 The Integrity Flow
Client → Request Nonce → Server > Client → Play Integrity API → Token > Client → Send Token → Server > Server → Decrypt & Verify → Apply Risk Rules
🛠️ Implementation: The Tiered Integrity Strategy
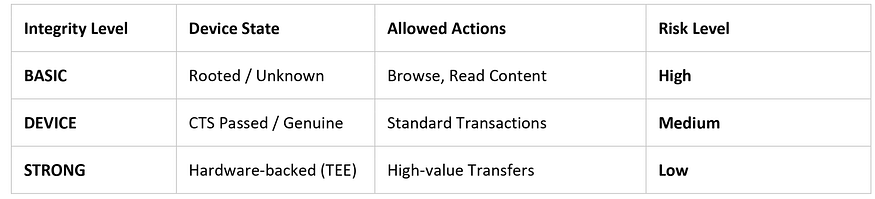
A Staff-level architect avoids “all-or-nothing” security. We implement a Tiered Enforcement model based on the risk of the user’s action.
📊 Integrity Level Decision Table
Step 1: Requesting the Integrity Token (Kotlin)
We must pass a Nonce from our server to prevent replay attacks and ensure freshness.
// 1. Fetch a cryptographically random Nonce from your backend
// The backend should store this nonce and mark it as 'pending'
val nonce: String = backend.getIntegrityNonce()
val integrityManager = IntegrityManagerFactory.create(applicationContext)
val integrityTokenRequest = IntegrityTokenRequest.builder()
.setNonce(nonce)
.build()
lifecycleScope.launch {
try {
val response = integrityManager.requestIntegrityToken(integrityTokenRequest).await()
val token = response.token()
// 2. Send token to backend. Verification MUST happen server-side.
backend.verifyDeviceIntegrity(token)
} catch (e: IntegrityServiceException) {
// Handle failures: Device may lack Play Services or have network issues
handleIntegrityFailure(e)
}
}🔍 Deep Dive: Strict Backend Validation
Crucial Rule: Never verify the integrity token on the client. Your backend must use the Google Play Developer API to decrypt the token and perform these mandatory checks:
- Nonce Validation: Ensure the nonce in the token matches the one issued for this session and has not been used before.
- Package Name Verification: Ensure the
packageNamein the token matches your official app ID exactly. - Certificate Digest Verification: Ensure the app signing certificate matches your official release key.
- Timestamp Verification: Check the timestamp inside the token to ensure the verdict is recent (e.g., within the last few minutes).
🚫 Common Implementation Mistakes
- Verifying tokens on the client: This is easily bypassed by runtime hooking.
- Reusing nonces: This opens the door for replay attacks where an old “clean” token is used on a now-compromised device.
- Hard-blocking all rooted devices: This creates massive user friction for “Power Users” who may not be malicious.
- Quota Exhaustion: Calling the API on every network request instead of at high-risk checkpoints.
⚠️ When NOT to Use Play Integrity
- Offline-First Apps: The API requires a network connection to verify with Google.
- Developer-Centric Apps: If your audience is 90% Custom ROM users, strict integrity checks will break your core UX.
- Low-Risk Applications: If you are building a simple utility app, the friction and latency of attestation may outweigh the security benefits.
🏁 Key Takeaways
- Environmental Trust is the foundation. Without it, your logic is running in an untrusted sandbox.
- Tiered Risk: Align integrity requirements with business risk to minimize user friction.
- Dynamic Threats: Play Integrity helps detect runtime tampering and untrusted environments (dynamic analysis threats), but it must be part of a defense-in-depth strategy.
🙋♂️ Frequently Asked Questions (FAQs)
Can an attacker spoof ‘MEETS_STRONG_INTEGRITY’?
Because “Strong Integrity” relies on hardware-backed keys, it is designed to be highly resistant to spoofing. It is the highest level of device attestation Android provides.
Does this replace R8?
No. R8 protects your code from static analysis. Play Integrity protects your app from dynamic analysis. You need both for mobile app security Android excellence.
💬 Join the Discussion
- How do you handle the UX when a legitimate user fails a device integrity check?
- Have you implemented a tiered risk model, or do you take an “All or Nothing” approach?
In Part 6, we move deeper into runtime security — handling token lifecycle, race conditions, and advanced concurrency in network layers using the Interceptor Pattern.
📘 Master Your Next Technical Interview
Since Java is the foundation of Android development, mastering DSA is essential. I highly recommend “Mastering Data Structures & Algorithms in Java”. It’s a focused roadmap covering 100+ coding challenges to help you ace your technical rounds.
- E-book (Best Value! 🚀): $1.99 on Google Play
- Kindle Edition: $3.49 on Amazon
- Also available in Paperback & Hardcover.



.jpg)
Comments
Post a Comment