Part 9: Zero Trust - Device Binding & Risk Signals
Prevent account takeovers by binding session tokens to hardware-backed keys and implementing DPoP-inspired proof of possession.
In Part 8, we hardened the network pipe. But what if an attacker steals a valid session token directly from a compromised device or via a sophisticated phishing attack?
In a Zero Trust architecture, we stop trusting the session token as a standalone proof of identity. Instead, we treat every request as potentially hostile until it passes a multi-factor “Risk Check.” Today, we implement the ultimate defense against Account Takeover (ATO): Device Binding & Intelligent Risk Signals.
🔐 The Core Concept: Session ≠ Device
The traditional approach is binary: If the request has a valid Bearer token, let it through.
The Senior Approach is rigorous: A token is only valid if it is presented by the exact hardware to which it was originally issued.
⚡ TL;DR
- The Problem: Token theft (Sidejacking), where an attacker uses a stolen
access_tokenon a different machine. - The Solution: Device Binding using Android Keystore keys (preferably hardware-backed) and Refresh Token Rotation.
- The “Staff” Twist: A DPoP-inspired model binding the signature to the HTTP method, path, and body hash.
- Risk Signals: Detecting GeoIP, ASN (ISP), and Geo-velocity anomalies in real-time.
🔍 Threat Model: What Device Binding Stops
Before we code, let’s look at the “Kill Chain” this architecture disrupts:
- Stolen Bearer Tokens: Prevents replay from exported tokens because the original non-exportable signing key cannot be moved to an attacker’s machine.
- Endpoint Swapping: By signing the URL and Method, an attacker cannot “reuse” a signature for a
GET /balancerequest to authorize aPOST /transfer. - Phishing Session Reuse: Detects when a session is opened in a new, unrecognized “Persona.”
- Impossible Travel Fraud: Flags sessions that appear in geographically distant locations too quickly.
🏛️ Android Device Binding with Keystore
We implement a Proof-of-Possession model using secure hardware. When a user logs in, the app generates a unique key pair in the Android Keystore.
🔐 Android Key Attestation Backend Validation
For high-risk flows, simply receiving a public key isn’t enough. The backend validates the Google attestation certificate chain and inspects the attestation extension to confirm:
- Verified Boot State: Is the OS untampered?
- Patch Levels: Is the device running current security updates?
- Security Level: Does the key live in the TEE or StrongBox?
🛠️ Implementation: DPoP-Inspired Proof of Possession (Kotlin)
/**
* Generates a bank-grade signature binding the request to the hardware.
* We sign the Method, Path, Nonce, Timestamp, and Body Hash.
*/
fun signRequest(
method: String,
path: String,
nonce: String,
timestamp: Long,
bodyHash: String
): String {
val keyStore = KeyStore.getInstance("AndroidKeyStore").apply { load(null) }
val privateKey = keyStore.getKey("device_binding_key", null) as PrivateKey
// Binding the signature to the specific request context
// Format: "METHOD|PATH|NONCE|TIMESTAMP|BODY_HASH"
val signaturePayload = "$method|$path|$nonce|$timestamp|$bodyHash"
val signatureBytes = Signature.getInstance("SHA256withECDSA").run {
initSign(privateKey)
update(signaturePayload.toByteArray())
sign()
}
return Base64.encodeToString(signatureBytes, Base64.NO_WRAP)
}🚨 GeoIP Risk Engine for Session Hijacking
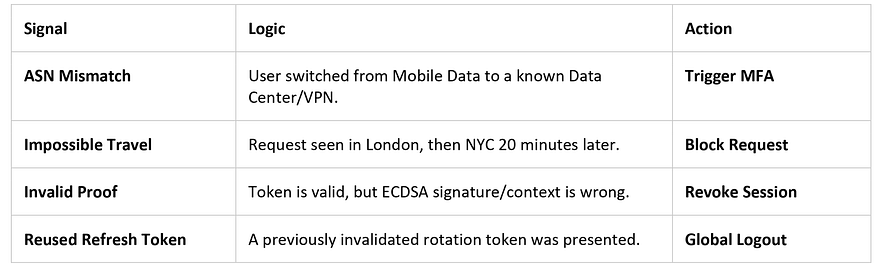
A Zero Trust backend doesn’t just “Allow” or “Block.” It adapts based on the severity of the signal:
Timestamp Validation: Reject proofs older than 60 seconds and allow a maximum ±30 second clock skew to prevent delayed replay attacks.
🛡️ Refresh Token Rotation with Reuse Detection
If a refresh_token is stolen, the attacker has long-term access.
Refined Logic: Every time a refresh_token is exchanged, the server invalidates the old token and issues a new one.
- Hashed Storage: Store refresh tokens as hashed server-side records. This ensures that even if your database is leaked, the raw tokens remain protected.
- Detection: If both the user and an attacker try to use the same
refresh_token, the server detects the "double-use" and kills the entire session for safety.
🏁 Key Takeaways
- Tokens are transferable; hardware is not. Bind your identity to the TEE/StrongBox.
- Context Matters. Sign the Method, Path, and Body Hash to prevent request manipulation.
- Rotate and Hash. A leaked refresh token should be single-use and unreadable in your logs.
🙋♂️ Frequently Asked Questions (FAQs)
Doesn’t signing every request add massive latency?
Hardware-backed ECDSA signing is highly efficient, typically taking 10–30ms. For standard API calls, this is a negligible price for bank-grade security.
How do you handle IP changes on mobile data?
Don’t block on simple IP changes. Look at the ASN (Provider). Switching from T-Mobile to home Wi-Fi is normal; switching to a known proxy or data center is a high-risk signal.
💬 Join the Discussion
- How do you balance security friction (MFA prompts) with user experience?
- Have you implemented Key Attestation? What were the challenges with backend verification?
📘 Master Your Next Technical Interview
Since Java is the foundation of Android development, mastering DSA is essential. I highly recommend “Mastering Data Structures & Algorithms in Java”. It’s a focused roadmap covering 100+ coding challenges to help you ace your technical rounds.
- E-book (Best Value! 🚀): $1.99 on Google Play
- Kindle Edition: $3.49 on Amazon
- Also available in Paperback & Hardcover.



.jpg)
Comments
Post a Comment